News
We are aware of the reported global cybersecurity incident involving Instructure, the vendor behind Canvas (Bruin Learn and UCLA Extension Canvas). We are actively monitoring vendor updates and assessing any potential impact to UCLA services.
At this time, UCLA has not been notified of any direct impact to our campus. Bruin Learn remains available and operational.
Updates will be posted on our Security Advisory Page and Service Status Page.
A new Linux kernel vulnerability, "Copy Fail" (CVE-2026-31431), allows local users to gain root access by writing four bytes into the page cache of readable files.
- Impact: Local Privilege Escalation (LPE) to root.
- Scope: Affects Linux kernels 4.14 and later (since 2017).
- Distributions: Impacted systems include Ubuntu, RHEL, Amazon Linux, and SUSE.
Recommended Action
Immediate patching is required. If patching is not possible, apply module-level mitigations as specified by your distribution's security advisory.
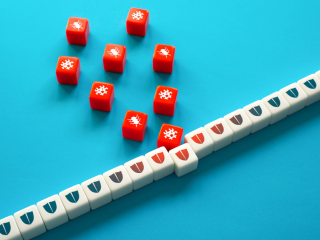
Imagine 1,000 prank callers dialing your phone at the same time. You’d never hear from the people who really needed to reach you. That’s essentially how a Distributed Denial of Service (DDoS) attack works. Instead of phone lines, attackers target websites or online services, hijacking devices and commanding them to flood a site with fake requests.
When people think of cyberattacks, they often imagine shadowy hackers breaking in from the outside. But some of the most damaging threats actually come from within. Insider threats — whether accidental, careless, or intentional — can expose sensitive data, disrupt operations and put the entire UCLA community at risk.